Introduction:
SailPoint IdentityIQ is a J2EE Application that is built on top of Hibernate object-relational model. All the Dev Artifacts are Java Objects represented in XML. The current blog discusses the script which helps in
- Migrating Artifacts to higher environments
- Migrating standard libraries
Working:
Below are the steps describing working of the script:
- The script will export objects from one IdentityIQ Environment through console attached to the instance (Console is a command line utility to each identityIQ instance provided).
- Script will perform necessary processing on the exported objects and prepares to be imported to the Target Environment.
- The Objects will be imported into the Target Environment through console attached to the instance.
Usage:
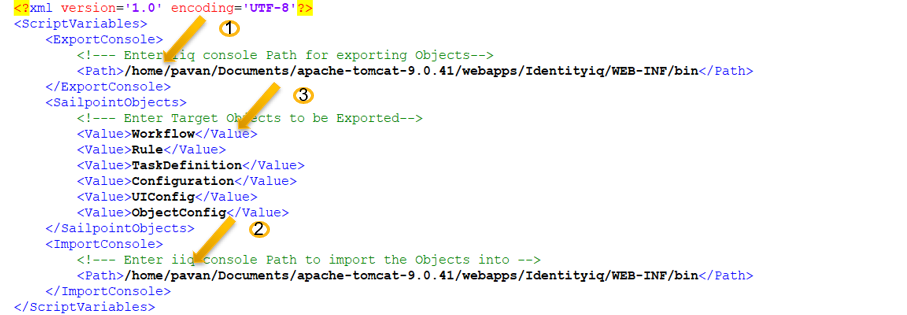
- Configure the Config.xml file provided with the following parameters
- Export Console Path
- Import Console Path
- Required Objects
- Run the script provided.
Below is the Demo on Exporter script:



