In the world of Identity Management, securing and monitoring the access for the external users like partners, contractors and customers who have access to organizational resources have always been a challenge for many organizations. To mitigate and help the organizations to secure their resources two big Identity management products partnered together in February 2018. Okta and SailPoint announced a strategic partnership to provide an end-to-end identity for the enterprise – helping organizations balance providing simple, secure user access while meeting complex compliance and security requirements.
Benefits of the Combined Solutions
• Effectively manage user identities’ authentication, application assignments, while ensuring all governance and compliance requirements are met.
• Authenticate user access with single sign-on and multi-factor authentication.
• Ensure that for sensitive applications, only the right user has access, authorization policies are enforced, and the process is documented, timestamped and compliant.
• Automate provisioning throughout the user lifecycle by simplifying processes for creating, modifying and revoking access.
• Automate provisioning of applications adherent to corporate policies.
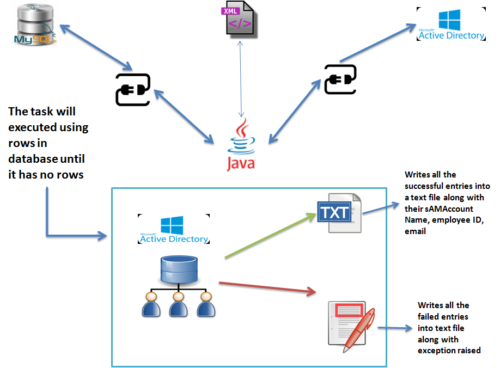
• Trigger provisioning workflows from authoritative sources, such as Active Directory or HR systems, to ensure consistency and increase efficiency.
Below presentation demonstrates Okta, IdentityIQ, SSO Concepts, Importance of SailPoint’s IdentityIQ integration to achieve SSO. The presentation is followed by a demo.
Okta and SailPoint IIQ Integration
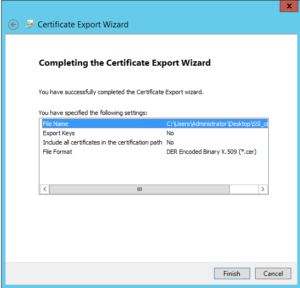
Demo of SailPoint’s IIQ and Okta Integration.